Your Whatsapp number is leaked in the open web

I have discovered this privacy issue in the WhatsApp web portal that leaked around 29000–300000 WhatsApp user’s mobile numbers in plaintext accessible to any internet user in plaintext.
I have discovered this privacy issue in the WhatsApp web portal that leaked around 29000–300000 WhatsApp user’s mobile numbers in plaintext accessible to any internet user in plaintext. The number of numbers accessible to you may differ due to Google bot crawl daily and its indexes are updated, also the search results vary in google.com, google.co.in and similar regional TLD’s. User’s affected are from United States, United Kingdom, India and almost all other countries. What makes this easy or appears to be simple is that data is accessible on the open web and not on the dark web.
Facebook removed the feature to search users with their phone numbers a year ago due to privacy risk and impact leaking phone numbers. Few days back, WhatsApp launched a new feature where friends can add you to their list by scanning a QR code. Every account is provided a unique QR code which when decoded shows a URL pointing to https://wa.me/
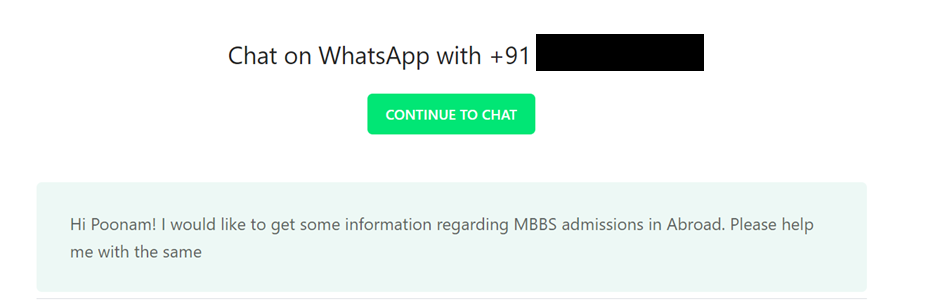
Whatsapp uses chat.whatsapp.com to generate group invite links while the Whatsapp Web send message API uses api.whatsapp.com and forwards the request to web.whatsapp.com.
Well, WhatsApp does also have a click to chat feature where the links are generated as https://wa.me/. This feature does not encrypt the phone number in the link, as a result, if this link is shared anywhere, your phone number is also visible in plaintext.
for example, you share this link with a friend on twitter to reach you on WhatsApp. Your mobile number is visible in plain text in this URL and anyone who gets hold of the URL can know your mobile number, you cannot revoke it.
Well after you share that tweet with your friend and you delete the tweet later, Google bot would have crawled the URL and the link would stay inthe web. This is because https://wa.me do not have a robots.txt file in its server root, which means you cannot stop Google or other search engine bots from crawling and indexing the wa.me links, which means those links will stay in the web. The pages do not have noindex meta tags to prevent any search engines from indexing the links.
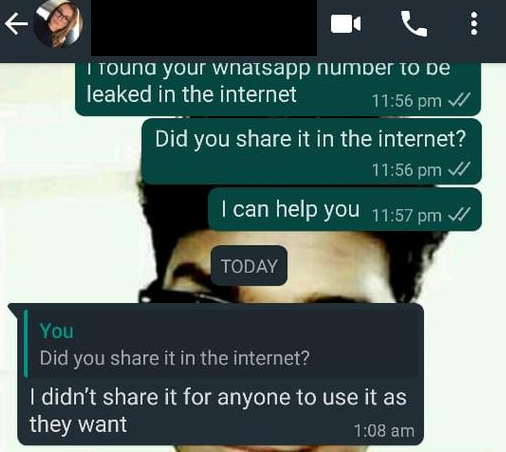
Well, the impact may be unknown people messaging you. Maybe they are marketing executives, cybercriminals, fraudsters targeting you. Depending on your Whatsapp privacy settings if the privacy settings are set to the public they may be already having your profile picture, name, profile status. As they have your mobile number, they may do SMS, Calls. The best way to avoid the situation maybe to delete your Whatsapp account or change your mobile number.
At the time of writing this article, Google search results showed me around 29000 results. As the Google bot crawls the results may differ.
Whatsapp users mobile numbers can be leaked using a simple google search query as such
https://www.google.com/search?q=site:wa.me
site:wa.me
To find numbers of a specific country, say the United States let’s add the country code
https://www.google.com/search?q=site%3Awa.me+%22%2B1%22
site:wa.me “+1”

India
https://www.google.com/search?q=site:wa.me+%22%2B91%22
site:wa.me “+91”
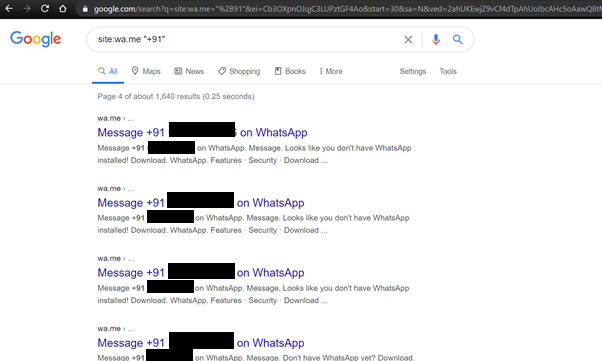
United Kingdom
site:wa.me “+44”
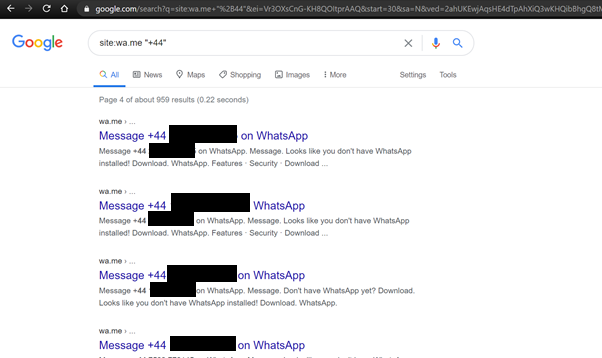
Similarly leaked whatsapp numbers of any country can be found using the google search query site:wa.me “<country_code>”
Observe that I have used the keyword site: which means only the google results originating from WhatsApp owned domain wa.me is shown and do not show any results from other blogs, or social media platforms. WhatsApp is a platform where each user is identified by a mobile number and not a username. Also unlike other social platforms you do not need to add someone as a friend to message others, getting to know a mobile number is enough to send a WhatsApp message.
Some stranger’s personal Whatsapp profile’s were identified and accessed to prove the validity of mobile numbers and show the impact. Most users do use the same profile picture on other social media accounts, the user profiles can be also easily find out.
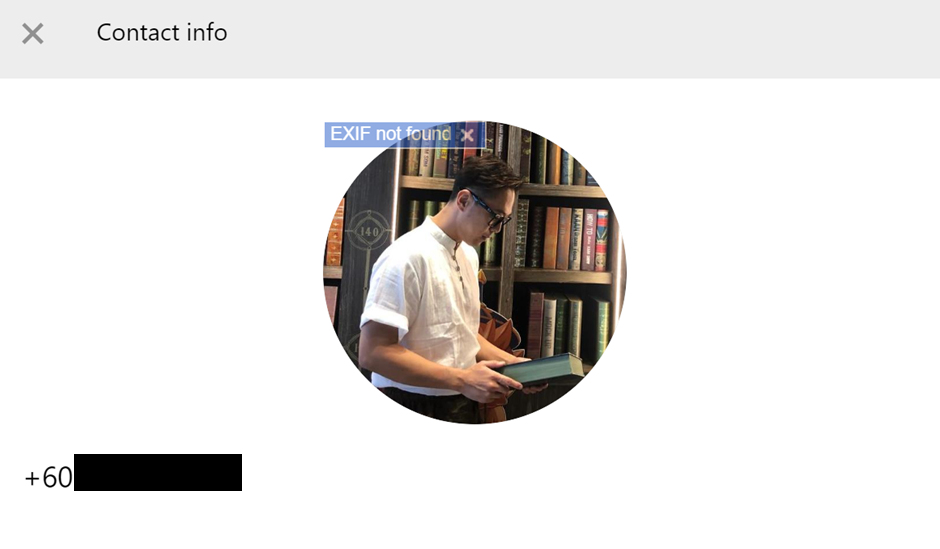
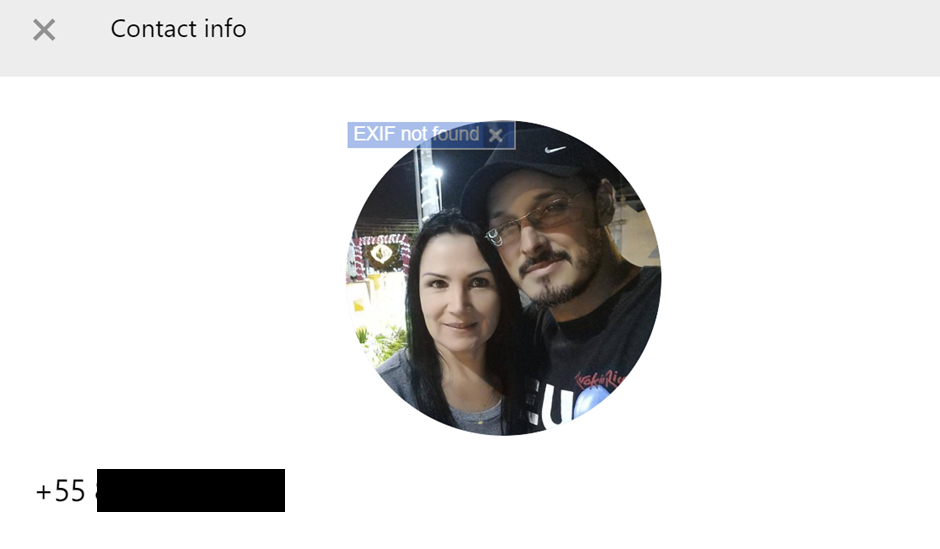
Profile pictures are shown as they set the visibility to public. As you can see they are personal accounts, not the business accounts, not the group chat invite links, not the new QR code format type of links.
Some users have their messages leaked as well, probably they used the Web API to communicate and those links got crawled.
And I tried to connect to few users to understand whether they shared number publicly on the social media or blogs.
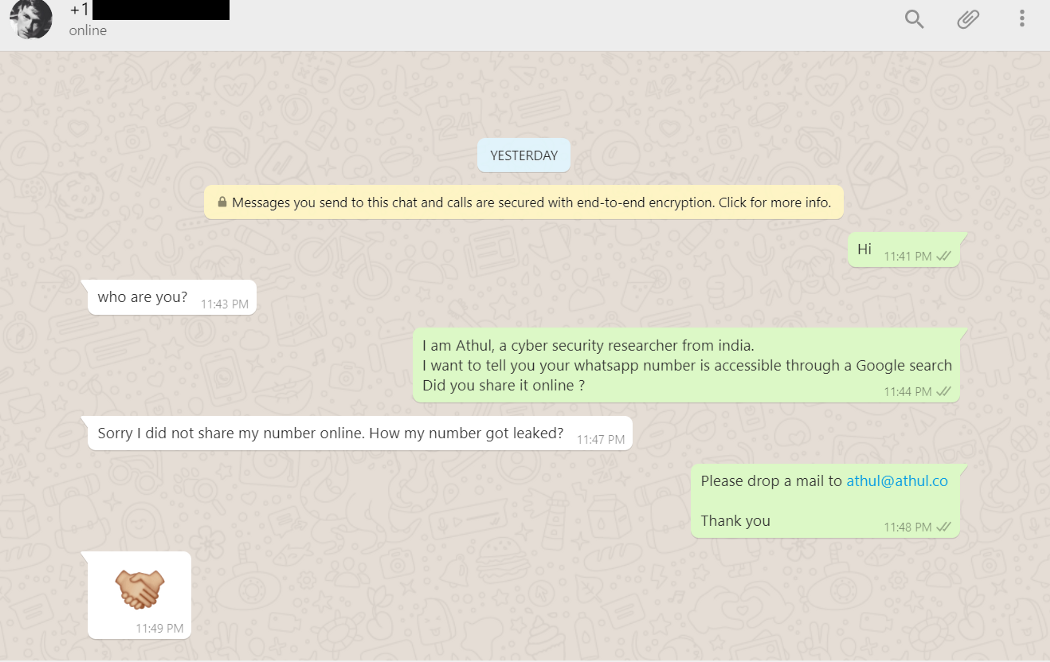
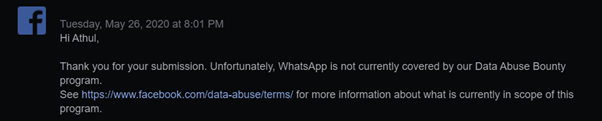
I have also contacted the Facebook team for which they have told me data abuse is only covered for Facebook platforms and not for WhatsApp seems they have to set privacy their priority. As someone who has worked with many bug bounty programs of many fortune 500 companies, I would say any leak of user data especially not of a single user but multiple users is a valid finding and has to be remediated.
With a big user base, they should care about these vulnerabilities. Today your mobile number is linked to your Bitcoin wallets, Aadhaar, bank accounts, UPI, Credit cards leading an attacker to perform SIM card swapping and cloning attacks by knowing your mobile number is another possibility.
Whether names of users are disclosed besides their mobile numbers?
On the whatsapp, their profile photos were able to seen as most users set the profile pictures to public in privacy settings.
On accessing the user profiles on whatsapp, the names of users were also visible if they have set About settings to everyone.
I am able to see their profile pictures as well as their names.
Suggested Fixes
- This privacy issue could have been avoided if Whatsapp encrypted or hashed the user mobile numbers. That is urls as such wa.me/1234567890 should be wa.me/EYVC8Zdsr35kVf8xCYNe29ebw6h4p4yu93 totally unpredictable and random. So even if it is shows up somewhere you cannot see the phone number in plaintext. [Not done yet by Whatsapp]
- The user should be also provided an option to revoke the click-to-chat links they have generated. In this manner, even if you shared the click-to-chat links with someone, you can revoke the link if you want to and no one else will be able to contact you. [Not done yet by Whatsapp]
- Add a meta noindex tag on the pages, this helps to prevent google search engine and other search engines from indexing the links and accessible to scammers or spammers like a 400000 phone numbers database in a a 1 second google search. [Done by Whatsapp after posting this article]
It is also observed that api.whatsapp.com has similar issues, so you can use same dorks for this domain as well. At one side Whatsapp promotes end to end encryption and atmost security (they claim) and the other side, they do not care about this.
Today, I made the web a safer place 😊. I fought for your privacy and we won . They removed as much as 400000 Whatsapp phone numbers from the web leaked from wa.me and api.whatsapp.com
This is a finding rejected by Facebook security team. I could have left it there as such as most bug bounty hunters do, but I couldn’t. I had to fight for your privacy and today you have it.
Dear Facebook Security team,
I believe you owe me something, a decent reward and a name in your hall of fame if you are fair, open and support privacy. I still believe we can work together in more findings as a team to find those unknown classes of bugs.
Many security researchers passed their observation that “this is a feature and not a bug”. I would like to say that to not to pass such negative comments on the internet atleast in the field of security research, everyone has different perceptions, internet is made for the betterment of humanity and to spread only love ❤️
As the leak occurred in Google, the fix was different. Let’s talk in simple terms. Data of website A users is available in website B with zero encryption, and that of 400000 users and increasing daily as the google bot crawlers finds more. If someone dumped this data and put in Pastebin, then the fix would have been to contact the support team of Pastebin and they would have deleted the data dump.
There were also users who have never ever shared their Whatsapp number on the internet. Only the Whatsapp team may be able to answer, how their numbers were leaked. Sorry, privacy did not exist!
“Anything that affects the security of a program or a system or a website/app can be termed a security bug. It just need to affect either the confidentality, integrity or availability” — Athul
Researchers need to think out of the box or better see as no box exist. You will observe so many guidelines in bug bounty programs what they accept, what they not. In case of an open ended research there are no limits, you decide the rules with only aim to protect the internet and it’s users from harm.